nrbroadcast file
# /etc/ax25/nrbroadcast # # The format of this file is: # # ax25_name min_obs def_qual worst_qual verbose # ax0 5 192 100 0 ax1 5 192 100 0 ax2 5 192 100 1 ax3 5 192 100 1 ax4 5 203 192 1 ax5 5 203 192 1 ax6 5 203 192 1
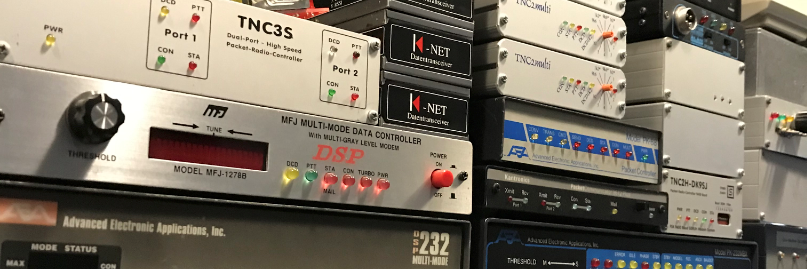
Packet-radio A Way Of Life
nrbroadcast file
# /etc/ax25/nrbroadcast # # The format of this file is: # # ax25_name min_obs def_qual worst_qual verbose # ax0 5 192 100 0 ax1 5 192 100 0 ax2 5 192 100 1 ax3 5 192 100 1 ax4 5 203 192 1 ax5 5 203 192 1 ax6 5 203 192 1
nrports file
# /etc/ax25/nrports # # The format of this file is: # #name callsign alias paclen description #---- -------- ----- ------ ----------- nr0 PI1LAP-5 LAPURO 236 Uronode PI1LAP-15 nr1 PI8LAP LAPBBS 236 Fbb BBS PI8LAP nr2 PI1LAP-4 LAPDX 236 DxSpider PI1LAP-4 nr3 PI1LAP-7 LAPPAC 236 FPAC node PI1LAP-7
ax25d.conf example file
# /etc/ax25/ax25d.conf
#
# ax25d Configuration File.
#
# AX.25 Ports begin with a '['.
#
[pi1lap-15 via ax0]
parameters 7 4 * * * * *
NOCALL * * * * * * L
default 7 2 2 60 300 5 - root /usr/local/sbin/uronode uronode
#
[lapuro via ax0]
parameters 7 4 * * * * *
NOCALL * * * * * * L
default 7 2 2 60 300 5 - root /usr/local/sbin/uronode uronode
#
[pi1lap-15 via ax1]
parameters 7 4 * * * * *
NOCALL * * * * * * L
default 7 2 2 60 300 5 - root /usr/local/sbin/uronode uronode
#
[lapuro via ax1]
parameters 7 4 * * * * *
NOCALL * * * * * * L
default 7 2 2 60 300 5 - root /usr/local/sbin/uronode uronode
#
[pi1lap-15 via ax2]
parameters 7 4 * * * * *
NOCALL * * * * * * L
default 7 2 2 60 300 5 - root /usr/local/sbin/uronode uronode
#
[lapuro via ax2]
parameters 7 4 * * * * *
NOCALL * * * * * * L
default 7 2 2 60 300 5 - root /usr/local/sbin/uronode uronode
#
[pi1lap-15 via ax3]
parameters 7 4 * * * * *
NOCALL * * * * * * L
default 7 2 2 60 300 5 - root /usr/local/sbin/uronode uronode
#
[lapuro via ax3]
parameters 7 4 * * * * *
NOCALL * * * * * * L
default 7 2 2 60 300 5 - root /usr/local/sbin/uronode uronode
#
[pi1lap-15 via ax4]
parameters 7 4 * * * * *
NOCALL * * * * * * L
default 7 2 2 60 300 5 - root /usr/local/sbin/uronode uronode
#
[lapuro via ax4]
parameters 7 4 * * * * *
NOCALL * * * * * * L
default 7 2 2 60 300 5 - root /usr/local/sbin/uronode uronode
#
[pi1lap-15 via ax5]
parameters 7 4 * * * * *
NOCALL * * * * * * L
default 7 2 2 60 300 5 - root /usr/local/sbin/uronode uronode
#
[lapuro via ax5]
parameters 7 4 * * * * *
NOCALL * * * * * * L
default 7 2 2 60 300 5 - root /usr/local/sbin/uronode uronode
#
[PI1LAP-7 via ax0]
NOCALL * * * * * * L
default * * * * * * - root /usr/local/sbin/fpacnode fpacnode -q %S
#
[LAPPAC via ax0]
NOCALL * * * * * * L
default * * * * * * - root /usr/local/sbin/fpacnode fpacnode -q %S
#
[PI1LAP-7 via ax1]
NOCALL * * * * * * L
default * * * * * * - root /usr/local/sbin/fpacnode fpacnode -q %S
#
[LAPPAC via ax1]
NOCALL * * * * * * L
default * * * * * * - root /usr/local/sbin/fpacnode fpacnode -q %S
#
[PI1LAP-4 via ax0]
parameters 2 1 6 900 * 15 0
NOCALL * * * * * * L
default * * * * * * - sysop /spider/src/client client %s ax25
#
[LAPDX via ax0]
parameters 2 1 6 900 * 15 0
NOCALL * * * * * * L
default * * * * * * - sysop /spider/src/client client %s ax25
#
[PI1LAP-4 via ax1]
parameters 2 1 6 900 * 15 0
NOCALL * * * * * * L
default * * * * * * - sysop /spider/src/client client %s ax25
#
[LAPDX via ax1]
parameters 2 1 6 900 * 15 0
NOCALL * * * * * * L
default * * * * * * - sysop /spider/src/client client %s ax25
#
[PI1LAP-4 via ax2]
parameters 2 1 6 900 * 15 0
NOCALL * * * * * * L
default * * * * * * - sysop /spider/src/client client %s ax25
#
[LAPDX via ax2]
parameters 2 1 6 900 * 15 0
NOCALL * * * * * * L
default * * * * * * - sysop /spider/src/client client %s ax25
#
[PI1LAP-4 via ax3]
parameters 2 1 6 900 * 15 0
NOCALL * * * * * * L
default * * * * * * - sysop /spider/src/client client %s ax25
#
[LAPDX via ax3]
parameters 2 1 6 900 * 15 0
NOCALL * * * * * * L
default * * * * * * - sysop /spider/src/client client %s ax25
#
#
# NET/ROM Ports begin with a '<'.
#
#
<nr2>
parameters 1 10 * * * * *
NOCALL * * * * * * L
default * * * * * * - sysop /spider/src/client client %s ax25
#
<nr0>
parameters 1 10 * * * 3 *
NOCALL * * * * * * L
default * * * * * * 0 root /usr/local/sbin/uronode uronode
#
<nr1>
default * * * * * * * root /usr/local/sbin/xfbbC -c -i %S
#
<nr3>
parameters 1 10 * * * * *
NOCALL * * * * * * L
default * * * * * * - root /usr/local/sbin/fpacnode fpacnode -q %S
#
{PI1LAP-15 via rose0}
default * * * * * * 0 root /usr/local/sbin/uronode uronode
axports file
# /etc/ax25/axports # # The format of this file is: # # name callsign speed paclen window description # ----- ----------- ------- ------- ------- --------------------------- ax0 PI1LAP-1 9600 128 4 144.850Mhz 1k2 ax1 PI1LAP-2 9600 128 4 430.950Mhz 9k6 ax2 PI1LAP-3 19200 256 4 Link local BBS pi8lap ax3 PI1LAP-6 19200 256 4 Link local Dx pi1lap-4 ax4 PI1LAP-8 19200 256 2 AX25/udp via pi1lap-8 ax5 PI1LAP-9 19200 256 2 AX25/ip via pi1lap-9 ax6 PD9Q-7 19200 256 2 Link local Jnos pd9q rose0 PI1LAP-11 9600 128 4 Rose port
Voorbeeld van port.sys die ik gebruik voor pi8lap
# BBS port.sys # # Number of Com Ports (not including Com 0) and TNCs 3 10 # # Interface 7 = TCPIP # Interface 9 = LINUX # #Com Interface Adress (Hex) Baud 1 9 0 115200 2 9 189C 0 3 9 189D:189E:77 0 # # Maxframe: The maximum number of frames the TNC will send at a time. # NbFwd : Number of channels for OUTGOING forward at the same time. # MxBloc : Size of forward-block in Kb. # # M/P-Fwd : Minute of the hour for start of forward, and period # (how many minutes between each forward-start). # Mode : One of these: # B : BBS-mode. # G : "Guest"-mode. # U : Normal-mode. # Type host-mode, one of these: # D : WA8DED # K : KAM hostmode. # M : Telephone-modem. # P : PK-232 # Q : BPQ v 4.x # Addition: One of these letters can be used too: # L : Send unproto beacon after each arriving mail. # Y : Yapp allowed on this QRG. # W : Gateway allowed TO this QRG. # R : Read-Only acces. # E : Recommanded by JP F6FBB # # Freq. : Text to describe this port (max 9 characters, no space) # Same number of lines as number of TNCs. # #TNC NbCh Com MultCh Pacln Maxfr NbFwd MxBloc M/P-Fwd Mode Freq 0 0 0 0 0 0 0 0 00/01 ---- File-fwd. 1 4 1 ax0 128 4 2 10 15/60 XULWY 144.850 2 4 1 ax1 128 4 2 10 15/60 XULWY 430.950 3 4 1 ax2 128 4 2 10 15/60 XULWY Node 4 10 2 0 250 7 4 10 15/15 TUY Telnet 5 10 1 nr1 250 4 2 10 30/15 XUWY NetRom 6 10 3 0 250 7 4 10 00/10 SU Pop/smtp 7 10 1 rose0 250 4 4 10 30/15 XUWY Rose 8 10 1 ax4 250 4 4 10 30/15 XUWY Axudp 9 10 1 ax5 250 4 4 10 30/15 XUWY Axip 10 10 1 ax6 250 4 4 10 30/15 XUWY Jnos # # Special callsigns and modes for some channels # TNC Nbs Callsign-SSID Mode # 1 2 XXXXX-1 B # # End of file
Traceroute from Windows machines typically uses ICMP Type 8 packets. Traceroute from Unixlike machines typically uses UDP packets with sequentially increasing destination ports, from 33434 to 33534. So your server (the traceroute destination) must not drop incoming ICMP Type 8 or UDP 33434:33534.
Here’s where it gets tricky: it really doesn’t need to accept those packets either, which the vast majority of sites addressing this issue recommends. It just needs to be able to reject them, which won’t happen if they’re being dropped. If you implement the typical advice – accepting those packets – traceroute basically ends up sort of working by accident: those ports shouldn’t be in use by any running applications, and since nothing is monitoring them, the server will issue an ICMP Type 3 response (destination unreachable). However, if you’re accepting packets to these ports, then a rogue application listening on those ports also becomes reachable – which is the sort of thing your firewall should be preventing in the first place.
The good news is, DROP and ACCEPT aren’t your only options – you can REJECT these packets instead, which will do exactly what we want here: allow traceroutes to work properly without also potentially enabling some rogue application to listen on those UDP ports.
So all you really need on your server to allow incoming traceroutes to work properly is:
# allow ICMP Type 8 (ping, ICMP traceroute) -A INPUT -p icmp --icmp-type 8 -j ACCEPT # enable UDP traceroute rejections to get sent out -A INPUT -p udp --dport 33434:33523 -j REJECT
Setup een amprnet gateway met policy based routing.
Neem een kijkje op deze website voor de uitleg.
http://wiki.ampr.org/wiki/Startampr
############# tunnel ampr.org ################################
ifconfig tunl0 up 44.137.31.65/27 multicast
ip tunnel change ttl 64 mode ipip tunl0
ip link set dev tunl0 up
################# default route naar gw-44-137.ampr.org ##################
ip route add default dev tunl0 via 213.222.29.194 onlink table 44
######################## route ampr.org #################################
ip rule add to 44.0.0.0/8 table 44 priority 44
ip rule add from 44.137.31.64/27 table 44 priority 45
# Xnet Route
ip route add 44.137.31.70 dev sl0 table 44 src 44.137.31.69
# Jnos Route
ip route add 44.137.31.67 dev tun0 table 44 src 44.137.31.68
ip rule add from 44.137.31.64/27 to 192.168.1.0/24 table main priority 22
ip rule add to 44.137.31.64/27 table main priority 44
ip rule add dev tunl0 table 44 priority 45
ip rule add dev eth0 table 44 priority 46
ip rule add from 44.137.31.64/27 table 44 priority 47
### STARTS THE ampr-ripd ROUTER DAMEON
# -s saves routes to /var/lib/ampr-ripd/encap.txt
# -r use raw socket instead of multicast
# -t routing table to use
# -i tunnel interface to use
# -p RIPv2 password (latest ampr-ripd defaults to the current valid password)
# -a ampr subnets to be ignored (remove your allocation from the table)
/usr/sbin/ampr-ripd -s -r -t 44 -i tunl0 -L pi1lap@jo11vn
Fanless, Intel® Core Duo, Entertainment Multimedia Engine
De oude Dell optiplex gx260 wordt vervangen door een Boxer AEC-6860. Deze draait op een 12v voeding. Dus hij kan mooi mee met de voeding voor de zenders en modems van pi1lap.
 i
i


root@pi1lap:~# traceroute -m 64 bad.horse traceroute to bad.horse (162.252.205.157), 64 hops max, 60 byte packets 18 bad.horse (162.252.205.130) 138.709 ms 140.816 ms 139.755 ms 19 bad.horse (162.252.205.131) 149.362 ms 148.325 ms 147.516 ms 20 bad.horse (162.252.205.132) 154.015 ms 150.660 ms 150.547 ms 21 bad.horse (162.252.205.133) 162.613 ms 152.024 ms 153.963 ms 22 he.rides.across.the.nation (162.252.205.134) 168.164 ms 167.627 ms 157.998 ms 23 the.thoroughbred.of.sin (162.252.205.135) 161.472 ms 165.656 ms 166.011 ms 24 he.got.the.application (162.252.205.136) 169.413 ms 168.101 ms 192.127 ms 25 that.you.just.sent.in (162.252.205.137) 187.624 ms 175.584 ms 174.123 ms 26 it.needs.evaluation (162.252.205.138) 187.203 ms 178.079 ms 188.922 ms 27 so.let.the.games.begin (162.252.205.139) 194.090 ms 190.662 ms 189.273 ms 28 a.heinous.crime (162.252.205.140) 192.752 ms 188.997 ms 193.715 ms 29 a.show.of.force (162.252.205.141) 202.382 ms 202.387 ms 203.915 ms 30 a.murder.would.be.nice.of.course (162.252.205.142) 234.657 ms 203.534 ms 200.304 ms 31 bad.horse (162.252.205.143) 206.686 ms 205.931 ms 205.938 ms 32 bad.horse (162.252.205.144) 211.575 ms 215.600 ms 218.457 ms 33 bad.horse (162.252.205.145) 216.021 ms 222.228 ms 222.077 ms 34 he-s.bad (162.252.205.146) 222.613 ms 229.693 ms 228.600 ms 35 the.evil.league.of.evil (162.252.205.147) 227.446 ms 235.141 ms 235.604 ms 36 is.watching.so.beware (162.252.205.148) 228.613 ms 229.605 ms 229.793 ms 37 the.grade.that.you.receive (162.252.205.149) 244.729 ms 238.574 ms 243.192 ms 38 will.be.your.last.we.swear (162.252.205.150) 243.546 ms 245.120 ms 238.522 ms 39 so.make.the.bad.horse.gleeful (162.252.205.151) 244.504 ms 244.750 ms 244.333 ms 40 or.he-ll.make.you.his.mare (162.252.205.152) 287.329 ms 258.506 ms 249.524 ms 41 o_o (162.252.205.153) 257.108 ms 259.796 ms 258.953 ms 42 you-re.saddled.up (162.252.205.154) 260.623 ms 260.135 ms 257.166 ms 43 there-s.no.recourse (162.252.205.155) 263.938 ms 263.962 ms 266.667 ms 44 it-s.hi-ho.silver (162.252.205.156) 284.177 ms 278.989 ms 271.777 m


ax0 voor link fbb
ax1 voor link Convers
eth0 Dit is de Baas
sl0 voor (X)net
tun0 voor Jnos
tunl0 voor ampr Gateway
Om te zorgen dat de data gaat lopen hebben we een aantal ip routes nodig.
ip route add 44.137.31.70 dev sl0 table 44 src 44.137.31.69
ip route add 44.137.31.67 dev tun0 table 44 src 44.137.31.82
En voor de iptables firewall
$ipt -A FORWARD -i tunl0 -o sl0 -j ACCEPT
$ipt -A FORWARD -i sl0 -o tunl0 -j ACCEPT
$ipt -A FORWARD -i tunl0 -o tun0 -j ACCEPT
$ipt -A FORWARD -i tun0 -o tunl0 -j ACCEPT
Met deze bovenstaande regels heeft iedereen toegang tot sl0 en tun0